What is SeLoadDriverPrivilege
 William Burgess
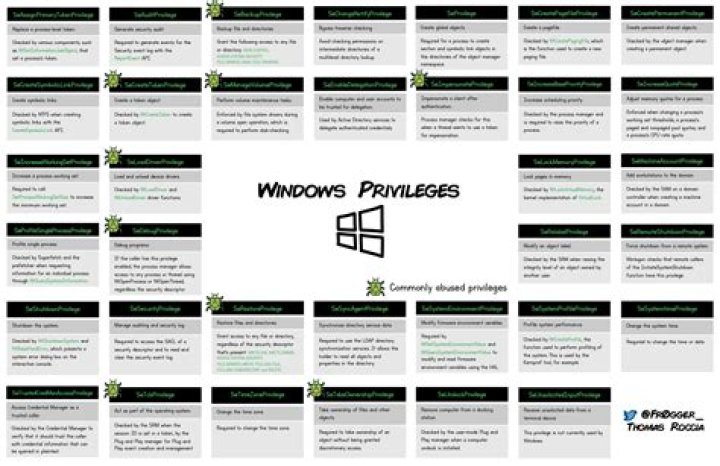
William Burgess SeLoadDriverPrivilege. Load and unload device drivers. Required to load or unload a device driver. With this privilege, the user can dynamically load and unload device drivers or other code in to kernel mode. This user right does not apply to Plug and Play device drivers.
What is SeTcbPrivilege used for?
Allows a process to assume the identity of any user and thus gain access to the resources that the user is authorized to access. Typically, only low-level authentication services require this privilege.
What is SeAuditPrivilege?
AKA: SeAuditPrivilege, Generate security audits. Note: This is an admin-equivalent right. Default assignment: Local System (This default assignment does not show up in Local Security Policy. It is implicit.) This extremely sensitive right allows you to report events to the security log using the ReportEvent() API.
What is SeRestorePrivilege?
SeRestorePrivilege allows file content modification, even if the security descriptor on the file might not grant such access. This function can also be used to change the owner and protection. SeChangeNotifyPrivilege allows traverse right. … In this case, the file system makes a policy decision to enforce this privilege.What is SeDelegateSessionUserImpersonatePrivilege?
SeDelegateSessionUserImpersonatePrivilege. In this instance, the user account was granted the SeDebugPrivilege as part of a logon event. This indicates the user token generated on this machine may be targeted and abused by a malicious actor with system access.
What is LsaRegisterLogonProcess?
The LsaRegisterLogonProcess function establishes a connection to the LSA server and verifies that the caller is a logon application.
What is a privileged service was called?
4673: A privileged service was called. Event 4673 indicates that the specified user exercised the user right specified in the Privileges field. Note: “User rights” and “privileges” are synonymous terms used interchangeably in Windows. Some user rights are logged by this event – others by 4674.
What is SeSystemEnvironmentPrivilege?
SeSystemEnvironmentPrivilege. Modify firmware environment values. Required to modify the nonvolatile RAM of systems that use this type of memory to store configuration information.What is bypass traverse checking permissions?
Bypass Traverse Checking determines which users can traverse directory or file system folder trees even though they might not have permissions on the level of the traversed directory or file system folder hierarchy itself.
How do I view Windows security event logs?- Open Event Viewer.
- In the console tree, expand Windows Logs, and then click Security. The results pane lists individual security events.
- If you want to see more details about a specific event, in the results pane, click the event.
Where are audit logs stored in Windows?
By default, Event Viewer log files use the . evt extension and are located in the %SystemRoot%\System32\Config folder. Log file name and location information is stored in the registry.
What is Token_privileges?
TOKEN_PRIVILEGES contains information about a set of privileges for an access token.
What is Seimpersonate?
verb (used with object), im·per·son·at·ed, im·per·son·at·ing. to assume the character or appearance of; pretend to be: He was arrested for impersonating a police officer. to mimic the voice, mannerisms, etc., of (a person) in order to entertain. to act or play the part of; personate.
What is LookupPrivilegeValue?
The LookupPrivilegeValue function retrieves the locally unique identifier (LUID) used on a specified system to locally represent the specified privilege name.
What is SeCreateGlobalPrivilege?
The “Create global objects” user right (SeCreateGlobalPrivilege) is a Windows 2000 security setting that was first introduced in Windows 2000 SP4. The user right is required for a user account to create global objects in a Terminal Services session.
What is Advapi logon process?
The logon process is marked as “advapi”, which means that the logon was a Web-based logon through the IIS web server and the advapi process. If you are not hosting IIS websites, this might mean that the computer is infected.
What is C Windows system32 lsass EXE?
In Microsoft Windows, the file lsass.exe in the directory c:\windows\system32 or c:\winnt\system32 is the Local Security Authority Subsystem Service. … It is a crucial component of Microsoft Windows security policies, authority domain authentication, and Active Directory management on your computer.
What is impersonate a client after authentication?
The “Impersonate a client after authentication” user right allows a program to impersonate another user or account to run on their behalf. An attacker could potentially use this to elevate privileges.
How do I replace a process level token?
- Login with your Administrator account on the Windows machine.
- Go to Control Panel and open the Administrative Tools.
- Open Local Security Policy and expand Local Policies.
- Under User Rights Assignment, open the Replace a Process Level Token.
What is adjust memory quotas for a process?
A user with the Adjust memory quotas for a process privilege can reduce the amount of memory that is available to any process, which could cause business-critical network applications to become slow or to fail. This privilege could be used by a malicious user to start a denial-of-service (DoS) attack.
What is a special logon?
The use of a special logon, which is a logon that has administrator-equivalent privileges and can be used to elevate a process to a higher level. A logon by a member of a Special Group. Special Groups enable you to audit events generated when a member of a certain group has logged on to your network.
What are tokens Windows?
When a user logs on, Windows creates an access token for this user. It is used to store a user’s identity and privileges. Such an access token stores the following information. The user’s SID (security identifier) The SIDs of the groups that the user belonged to when the user was authenticated.
What are the 3 types of logs available through the event viewer?
Types of Event Logs They are Information, Warning, Error, Success Audit (Security Log) and Failure Audit (Security Log).
How long are Windows event logs kept?
Data typeData pruning default settingLog inspection events7 daysApplication control events7 daysSystem eventsNeverServer logs7 days
How do I monitor Windows logs?
- From the Activity pane, drag a Monitor Event Log activity to the runbook.
- Double-click the Monitor Event Log activity icon to open the Properties dialog box.
- Configure the settings on the Details tab and on the Advanced tab.
How do I view file audit logs?
Navigate to the file/folder for which you want to view the audit logs. Click Audit Logs. Or right-click the file or folder and select Audit Logs. Apply the time filter for which you want to view the user activity on a specific file or folder.
What should audit logs contain?
- User IDs.
- Date and time records for when Users log on and off the system.
- Terminal ID.
- Access to systems, applications, and data – whether successful or not.
- Files accessed.
- Networks access.
- System configuration changes.
- System utility usage.
Is it safe to delete Windows log files?
It logs various pieces of information related to the Windows trusted installer, for example: the installation of windows updates. You can safely delete this file; the trusted installer creates a new one if it can’t find it.
What is AdjustTokenPrivileges?
The AdjustTokenPrivileges function enables or disables privileges in the specified access token. Enabling or disabling privileges in an access token requires TOKEN_ADJUST_PRIVILEGES access.
What is SeIncreaseWorkingSetPrivilege?
SeIncreaseWorkingSetPrivilege. Increase a process working set. Required to call SetProcessWorkingSetSize to increase the minimum working set. This indirectly allows the process to lock up to the minimum working set of memory using VirtualLock.
What is print spoofer?
PrintSpoofer exploit that can be used to escalate service user permissions on Windows Server 2016, Server 2019, and Windows 10. To escalate privileges, the service account must have SeImpersonate privileges. To execute: PrintSpoofer.exe -i -c cmd. With appropriate privileges this should grant system user shell access.