What is JWT authorization
 Andrew Campbell
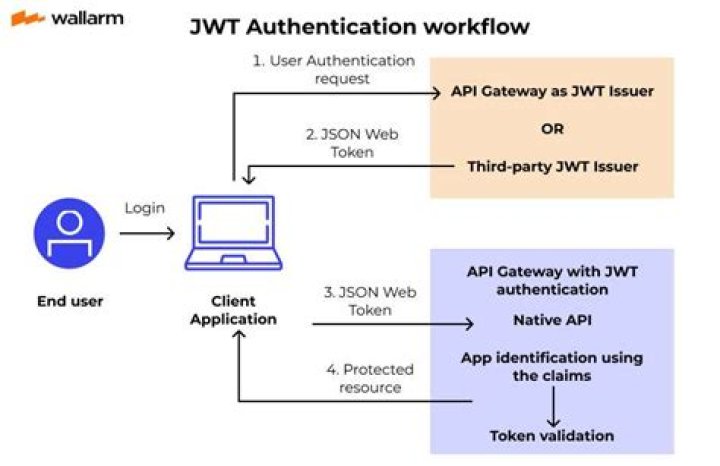
Andrew Campbell Authorization: This is the most common scenario for using JWT. Once the user is logged in, each subsequent request will include the JWT, allowing the user to access routes, services, and resources that are permitted with that token.
What is JWT Authorisation?
What is JWT Authentication? JSON Web Token (JWT) is a JSON encoded representation of a claim(s) that can be transferred between two parties. The claim is digitally signed by the issuer of the token, and the party receiving this token can later use this digital signature to prove the ownership on the claim.
How do I use JWT for authorization?
To authenticate a user, a client application must send a JSON Web Token (JWT) in the authorization header of the HTTP request to your backend API. API Gateway validates the token on behalf of your API, so you don’t have to add any code in your API to process the authentication.
Is JWT authentication or authorization?
JSON Web Token (JWT) is an open standard for securely transmitting information between parties as a JSON object. … JWT is commonly used for authorization. JWTs can be signed using a secret or a public/private key pair.Is JWT good for authorization?
JWT is a particularly useful technology for API authentication and server-to-server authorization.
Why is JWT used?
JWT, or JSON Web Token, is an open standard used to share security information between two parties — a client and a server. Each JWT contains encoded JSON objects, including a set of claims. JWTs are signed using a cryptographic algorithm to ensure that the claims cannot be altered after the token is issued.
How is JWT verified?
- Verify that the JWT contains three segments, separated by two period (‘. …
- Parse the JWT to extract its three components.
What is difference between OAuth and JWT?
Basically, JWT is a token format. OAuth is an standardised authorization protocol that can use JWT as a token. OAuth uses server-side and client-side storage. If you want to do real logout you must go with OAuth2.How is JWT secure?
There are two critical steps in using JWT securely in a web application: 1) send them over an encrypted channel, and 2) verify the signature immediately upon receiving it. The asymmetric nature of public key cryptography makes JWT signature verification possible.
What is the difference between authentication and authorization?Authentication vs. Authorization. So, what is the difference between authentication and authorization? Simply put, authentication is the process of verifying who someone is, whereas authorization is the process of verifying what specific applications, files, and data a user has access to.
Article first time published onIs JWT secure over HTTP?
No, JWT is not required when your server supports HTTPS. HTTPS protocol ensures that the request & response are encrypted on the both(client & server) the ends.
Does Facebook use JWT?
It provides an entry point: “/auth/facebook” that redirects to FBs and proceeds to the authentication. After that it acquires the AccessToken for the logged user and creates a JWT Token that returns to the client.
What if JWT token is stolen?
Generally speaking, this is nice, but what happens if your entire JWT is stolen? Because JWTs are used to identify the client, if one is stolen or compromised, the attacker has full access to the user’s account in the same way they would if the attacker had compromised the user’s username and password instead.
How JWT is used in API security?
JWT has a collection of data and it allows the API to transfer only secured data. JWT asserts identity associated with trust between the two communicating parties. The interactive application development helps to secure apps and enable secure interactions within applications. JWT helps to create and use tokens.
How long should a JWT last?
The JWT access token is only valid for a finite period of time. Using an expired JWT will cause operations to fail. As you saw above, we are told how long a token is valid through expires_in. This value is normally 1200 seconds or 20 minutes.
How are JWT signatures validated?
The private key is used to generate the signature whereas the public key is used to validate the signature. In this case the private key is only in possession of the authentication server who has generated the JWT token and we no longer need to distribute the private key.
What is JWT kids token?
kid is an optional header claim which holds a key identifier, particularly useful when you have multiple keys to sign the tokens and you need to look up the right one to verify the signature. Once a signed JWT is a JWS, consider the definition from the RFC 7515: 4.1.4. ” kid” (Key ID) Header Parameter.
What is JWT encode?
JWT (JSON Web Token; pronounced like the word “jot”) are tokens for sharing claims. Claims are encoded JSON objects that include some information about a subject and are often used in Identity Security applications to transfer information about a user.
Do you need JWT?
When do we need JWT? Since the token is signed by the server, and since the key is private, no-one is able to modify it. So, if a user has a token with “username”=”greg” in it, you can trust this user. … When a user issues a request with a JWT, we do not need to query the database to verify user credentials.
What is difference between bearer token and JWT?
JWTs are a convenient way to encode and verify claims. A Bearer token is just string, potentially arbitrary, that is used for authorization.
Why is JWT not encrypted?
Because JWTs are stateless, when a server-side application receives a JWT, it can validate it using only the “secret key” that was used to create it — thereby avoiding the performance penalty of talking to a database or cache on the backend, which adds latency to each request.
Can JWT be encrypted?
As we said above, JWT are not encrypted by default, so care must be taken with the information included inside the token. If you need to include sensitive information inside a token, then encrypted JWT must be used.
How do I secure my JWT?
- Intro. …
- JWTs used as Access Tokens. …
- What algorithms to use. …
- When to validate the token. …
- Always check the issuer. …
- Always check the audience. …
- Make sure tokens are used as intended. …
- Dealing with expiration, issued time and clock skew.
Is JWT a bearer?
RFC 7519: JSON Web Token JSON Web Token (JWT, RFC 7519) is a way to encode claims in a JSON document that is then signed. JWTs can be used as OAuth 2.0 Bearer Tokens to encode all relevant parts of an access token into the access token itself instead of having to store them in a database.
Can JWT be used without OAuth?
Don’t Leave JWT All Alone The simple fact is that JWTs are a great solution, especially when used in tandem with something like OAuth. Those benefits quickly disappear when used alone, and in many cases can result in worse overall security.
What is better than JWT?
PASETO, or Platform Agnostic Security Token is one of the most successful designs that is being widely accepted by the community as the best-secured alternative to JWT.
What is authorization give example?
Authorization is the process of giving someone the ability to access a resource. … For instance, accessing the house is a permission, that is, an action that you can perform on a resource. Other permissions on the house may be furnishing it, cleaning it, repair it, etc.
What is meant by authorization?
Authorization is the process of giving someone permission to do or have something. … Thus, authorization is sometimes seen as both the preliminary setting up of permissions by a system administrator and the actual checking of the permission values that have been set up when a user is getting access.
What are the three types of authentication?
Authentication factors can be classified into three groups: something you know: a password or personal identification number (PIN); something you have: a token, such as bank card; something you are: biometrics, such as fingerprints and voice recognition.
Can JWT be decoded?
A valid JWT can consist of just the header and payload sections. … By design, anyone can decode a JWT and read the contents of the header and payload sections. But we need access to the secret key used to create the signature to verify a token’s integrity.
Is JWT a TLS?
This paper is an overview of JSON Web Token (JWT) and Transport Layer Security (TLS) as two primary approaches for authentication of the things on the Internet. JSON Web Token (JWT) is used extensively today for authorization and authentication within the OAuth and the OpenId framework.