GSM is the most secured cellular telecommunications system available today. GSM maintains end-to-end security by retaining the confidentiality of calls and anonymity of the GSM subscriber. Temporary identification numbers are assigned to the subscriber's number to maintain the privacy of the user..
Consequently, what are the GSM security issues?
The security architecture of GSM was originally intended to provide security services such as anonymity, authentication, and confidentiality of user data and signaling information. Authentication of mobile users for the network. Confidentiality of user data and signaling information. Anonymity of subscriber's identity.
Secondly, what is the use of GSM? GSM is an open and digital cellular technology used for transmitting mobile voice and data services operates at the 850MHz, 900MHz, 1800MHz and 1900MHz frequency bands. GSM system was developed as a digital system using time division multiple access (TDMA) technique for communication purpose.
Besides, what is GSM authentication?
GSM Evolution. Authentication is a process of exchanging information between a communications device and the mobile network which allows the carrier or network operator to confirm the true identity of the user (or device).
Is GSM encrypted?
5 Answers. For the most part they are encrypted, but not sufficiently enough to be considered as safe, tap resistant encryption. GSM uses 64-bit A5/1 encryption that is weak, to say the least. 3G networks use the KASUMI block cipher instead of the older A5/1 stream cipher.
Related Question Answers
What are the functions of authentication and encryption in GSM?
? The security mechanisms specified in the GSM standard make it the most secure cellular telecommunications system available. The use of authentication, encryption, and temporary identification numbers ensures the privacy and anonymity of the systems users, as well as safeguarding the system against fraudulent use.What is a3 authentication?
A3 - Authentication Algorithm A3. This variable is used by the network to authenticate a MS (Mobile Station) requesting network resources.How does cellular authentication work?
based digital cellular networks that are based on GSM technology (although they may appear under a different name). The basic approach to authentication is a challenge response method whereby the network sends a random value and the phone has to encrypt it with its secret key and send it back for verification.Which algorithm is used in calculation of SRES signed response in HSS?
The MS computes the 32-bit Signed Response (SRES) based on the encryption of the RAND with the authentication algorithm (A3) using the individual subscriber authentication key (Ki). Upon receiving the SRES from the subscriber, the GSM network repeats the calculation to verify the identity of the subscriber.What is a3 algorithm in GSM?
The A3 ciphering algorithm is used to authenticate each mobile by verifying the user password within the SIM with the cryptographic key at the MSC. The A5 ciphering algorithm is used for encryption. It provides scrambling for 114 coded bits sent in each TS. The A8 is used for ciphering key.How is GSM measured?
The term “GSM” stands for “grams per square meter.” For this standard, the weight of various types of paper is measured from a sample sheet cut to one square meter in size. No matter the length or width the paper becomes, the weight measurement is always taken from the square meter sheet.Is GSM a 4g?
LTE (Long Term Evolution) is a 4G communication standard designed to be 10x faster than standard 3G. GSM is a digital cellular technology used to transmit data and voice communication at a frequency range of 850MHz to 1900MHz. GSM technology uses a Time Division Multiple Access (TDMA) technique to transmit data.Why is GSM important?
Basically, GSM was built to aid 2g connectivity in mobile phones. Earlier, the network incorporated a circuit switching network but with time and need, it had to collaborate with GPRS, implementing the packet switching protocol. The frequency of operation of the GSM network falls within the range of 900-1800 MHz.What are the advantages of GSM?
Advantages of GSM: The accessibility of Subscriber Identity Modules (SIM cards), which are smart cards; provide secure data encryption to give GSM m-commerce advantages. GSM service is in more than 200 different countries, so it is quite easy to simply use your GSM phone when you are in one of these countries.What is the full meaning of GSM?
global system for mobile communication
What is GSM unit?
GSM is an acronym standing for 'Grams per Square Meter'. Quite simply, it allows print buyers and print suppliers to know exactly about the quality of paper that is being ordered. The higher the GSM number, the heavier the paper.Is GSM still used?
The difference will remain in any phone that needs to access an older 2G or 3G network. But the CDMA/GSM split will still exist in any area where 2G or 3G networks are still alive. In the US, Verizon plans to turn off 2G and 3G at the end of 2019. T-Mobile will turn off 2G and 3G at the end of 2020.What is GSM thickness?
The term GSM refers to the substance weight of paper, relating to an area of paper that remains constant, irrespective of sheet size, expressed as grams per square metre. Typically the higher the GSM the heavier (and generally, the thicker) the paper but this isn't always the case.What is meant by LTE?
LTE is an abbreviation for Long Term Evolution. LTE is a 4G wireless communications standard developed by the 3rd Generation Partnership Project (3GPP) that's designed to provide up to 10x the speeds of 3G networks for mobile devices such as smartphones, tablets, netbooks, notebooks and wireless hotspots.Can you hack a phone by calling it?
Your phone can be hacked by any hacker just knowing your phone number. You don't have to answer anything. They have your number and then they can listen to your phone calls read your texts and even find your location. But yes whether you accept a call or not they only just need the phone number.Can cell towers be hacked?
Attackers Hijack Cellular Phone Towers Thanks To Critical Flaws. No, this is not an empty threat because, security researchers from the mobile security firm, Zimperium have discovered three serious security flaws in BTS stations which can allow potential hacker remotely hijack the entire cell phone tower.Can 2g phones be hacked?
Weakness of 2G mobile phone networks revealed. The encryption scheme used for second generation (2G) mobile phone data can be hacked within seconds by exploiting weaknesses and using common hardware, researches at Agency for Science, Technology and Research (A*STAR), Singapore, show.Is CDMA more secure than GSM?
In CDMA technology, More security is provided as compared with the GSM technology because encryption is inbuilt in the CDMA. Therefore, the CDMA phone calls are more secure than the GSM calls. In terms of encryption, the GSM technology has to be upgraded so as to make it operate more securely.How do I decrypt my phone?
Manually decrypting an Android device On the Android that you want to decrypt, go to Settings > Security, and turn off encryption. The device must restart to complete the operation. Androids that do not have a decryption option: for example, Nexus 5 Android devices. 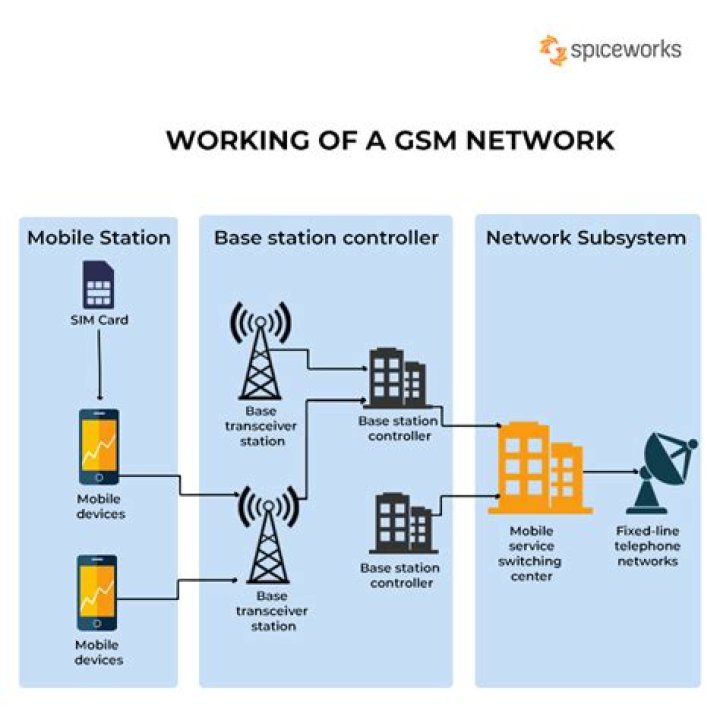
 Andrew Campbell
Andrew Campbell