How do you conduct AWS vulnerability scanning
 Christopher Lucas
Christopher Lucas Choose an AWS vulnerability scanner. Historically, AWS required express permission to run any form of vulnerability assessment on servers within the AWS infrastructure. … Run the scan to identify risks. … Analyze results and address vulnerabilities.
What are the three steps to conduct proper AWS vulnerability scanning?
- Choose an AWS vulnerability scanner. Historically, AWS required express permission to run any form of vulnerability assessment on servers within the AWS infrastructure. …
- Run the scan to identify risks. …
- Analyze results and address vulnerabilities.
How is vulnerability scanning done?
A vulnerability scanning service uses piece of software running from the standpoint of the person or organization inspecting the attack surface in question. … The findings in the report can then be analyzed and interpreted in order to identify opportunities for an organization to improve their security posture.
Can I vulnerability scan AWS?
Customers are only allowed to scan their own instances; they are not permitted to do testing against any AWS service itself (i.e. you cannot scan S3 or the EC2 API endpoints). … instances from scanning to prevent impact to these hosts; therefore, Alert Logic® does not recommend scanning of these instance types.Is AWS inspector a vulnerability scanner?
The new Amazon Inspector is a vulnerability management service that continually scans AWS workloads for software vulnerabilities and unintended network exposure is generally available, globally.
What is golden image AMI?
A golden AMI is an AMI that contains the latest security patches, software, configuration, and software agents that you need to install for logging, security maintenance, and performance monitoring.
How do I scan AWS environment?
- Make sure you meet the AWS scanning requirements.
- Submit your AWS regions for scanning by hitting the Add Scanning Target button in the Scanning\Scanning Targets section of the web console.
What is AWS xray?
AWS X-Ray is a service that helps developers analyze and debug distributed applications. Customers use X-Ray to monitor application traces, including the performance of calls to other downstream components or services, in either cloud-hosted applications or from their own machines during development.What is vulnerability scanning and what are the two different types of vulnerability scans?
There are two approaches to vulnerability scanning, authenticated and unauthenticated scans. In the unauthenticated method, the tester performs the scan as an intruder would, without trusted access to the network. Such a scan reveals vulnerabilities that can be accessed without logging into the network.
Are you permitted to conduct your own vulnerability scans on your own VPC without alerting AWS first?Are you permitted to conduct your own vulnerability scans on your own VPC without alerting AWS first? no. Security Groups operate at the instance level, they support “allow” rules only, and they evaluate all rules before deciding whether to allow traffic.
Article first time published onHow do you identify vulnerability scanning?
A vulnerability scan only identifies vulnerabilities, while a penetration tester digs deeper to identify the root cause of the vulnerability that allows access to secure systems or stored sensitive data. The pen tester also looks for business logic vulnerabilities that might be missed by an automatic scanner.
What are the types of vulnerability scans?
- Network-based scanners. Network based vulnerability scanners identify possible network security attacks and vulnerable systems on wired or wireless networks. …
- Host-based scanners. …
- Wireless scanners. …
- Application scanners. …
- Database scanners.
What is the best vulnerability scanner?
- Tenable Nessus. Tenable shares scanners, schedules, scan policies, and results between different teams with customization of workflows for efficient network vulnerability management.
- Rapid7 Nexpose. …
- Tripwire IP360. …
- OpenVAS. …
- CrowdStrike Falcon.
What are biggest AWS security vulnerabilities?
- 1) Overuse of Public Subnets. Many organizations use the default Virtual Private Cloud (VPC) built into AWS, making few changes to the configuration. …
- 2) IAM Issues. …
- 3) Misconfigured S3 buckets. …
- 4) Exposed Database Origin Servers. …
- 5) Server-Side Request Forgery (SSRF) …
- 6) Hanging DNS Records.
Is AWS inspector only for EC2?
Currently, Amazon Inspector Classic assessment targets can consist only of EC2 instances. You can run an agentless assessment with the Network Reachability rules package on any EC2 instances regardless of operating system.
What is AWS security scanner?
It enables you to analyze and manage usage, cost, security, and compliance of your AWS platform from one place and in real-time. Provides you with the visibility of all the services you are using. Identify and address vulnerabilities as well as compliance issues in the AWS configurations and environment.
What is meant by vulnerability assessment?
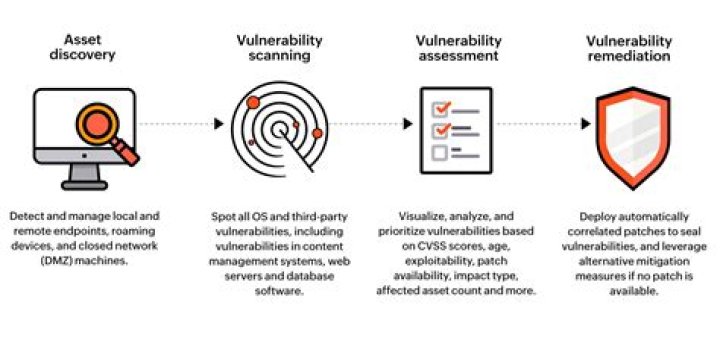
A vulnerability assessment is a systematic review of security weaknesses in an information system. It evaluates if the system is susceptible to any known vulnerabilities, assigns severity levels to those vulnerabilities, and recommends remediation or mitigation, if and whenever needed.
What is Shield in AWS?
AWS Shield is a managed Distributed Denial of Service (DDoS) protection service that safeguards applications running on AWS. AWS Shield provides always-on detection and automatic inline mitigations that minimize application downtime and latency, so there is no need to engage AWS Support to benefit from DDoS protection.
How do you conduct AWS security audit?
- When you should perform a security audit.
- Guidelines for auditing.
- Review your AWS account credentials.
- Review your IAM users.
- Review your IAM groups.
- Review your IAM roles.
- Review your IAM providers for SAML and OpenID Connect (OIDC)
- Review Your mobile apps.
What is AMI factory?
AMI Factory is an automation tool deployed in the customer’s account that enables them to continuously build, test, and validate AMIs. With Capgemini’s AMI Factory consulting offer, customers will be able to create AMIs with a secured, fast, and auditable process.
What is EC2 image builder?
EC2 Image Builder simplifies the building, testing, and deployment of Virtual Machine and container images for use on AWS or on-premises. … Image Builder is offered at no cost, other than the cost of the underlying AWS resources used to create, store, and share the images.
What is CodePipeline AWS?
AWS CodePipeline is a fully managed continuous delivery service that helps you automate your release pipelines for fast and reliable application and infrastructure updates. … With AWS CodePipeline, you only pay for what you use. There are no upfront fees or long-term commitments.
Is a vulnerability scanner a tool?
Web Application Vulnerability Scanners are automated tools that scan web applications, normally from the outside, to look for security vulnerabilities such as Cross-site scripting, SQL Injection, Command Injection, Path Traversal and insecure server configuration.
When should you run a vulnerability scan?
Overall, an industry best practice is to perform vulnerability scanning at least once per quarter. Quarterly vulnerability scans tend to catch any major security holes that need to be assessed, but depending on your unique organizational needs, you may end up performing scans monthly or even weekly.
What is the main difference between vulnerability scanning?
Vulnerability scans look for known vulnerabilities in your systems and report potential exposures. Penetration tests are intended to exploit weaknesses in the architecture of your IT network and determine the degree to which a malicious attacker can gain unauthorized access to your assets.
What is cold start in AWS?
A “cold start” is the 1st request that a new Lambda worker handles. This request takes longer to process because the Lambda service needs to: find a space in its EC2 fleet to allocate the worker. initialize the worker.
What is code star in AWS?
AWS CodeStar is a cloud‑based development service that provides the tools you need to quickly develop, build, and deploy applications on AWS. With AWS CodeStar, you can set up your entire continuous delivery toolchain in minutes, allowing you to start releasing code faster.
What are AWS traces?
AWS X-Ray traces user requests as they travel through your entire application. It aggregates the data generated by the individual services and resources that make up your application, providing you an end-to-end view of how your application is performing.
How many elastic IP can you create?
You’re limited to five Elastic IP addresses.
What best describes AWS EC2?
Amazon Elastic Compute Cloud (Amazon EC2) provides scalable computing capacity in the Amazon Web Services (AWS) Cloud. … You can use Amazon EC2 to launch as many or as few virtual servers as you need, configure security and networking, and manage storage.
What are the five types of vulnerability assessment?
- Network-based scans.
- Host-based scans.
- Wireless scans.
- Database scans.
- Application scans.